Handbook on data protection in humanitarian action
What is the handbook on data protection in humanitarian action?
Protecting individuals' personal data is an integral part of protecting their life, integrity and dignity. Therefore, personal data protection is of fundamental importance for humanitarian organizations.
In suggesting how data protection principles should be applied by humanitarian organizations, this handbook builds on existing guidelines, working procedures and practices that have been established in humanitarian action in the most volatile environments and for the benefit of the most vulnerable victims of armed conflicts, other situations of violence, natural disasters, pandemics and other humanitarian emergencies (together "humanitarian emergencies").
Some of these guidelines, procedures and practices pre-date the advent and development of data protection laws, but they all are based on the principle of human dignity and the same concept of protection which underpin data protection law.
Key issues for data protection:
Blockchain - Digital identity - Connectivity as aid
Social media - Artificial intelligence
Blockchain
In recent years, "blockchain" has become a buzzword and various organizations, including in the humanitarian sector, are trying to find a use for this technology. It has been argued that blockchain could improve efficiency in humanitarian programmes involving, for example, financial transactions and supply tracing. It has also been suggested that blockchain could enhance transparency and trust in information integrity.
However, achieving such improvements could be offset by a number of practical and data protection challenges.
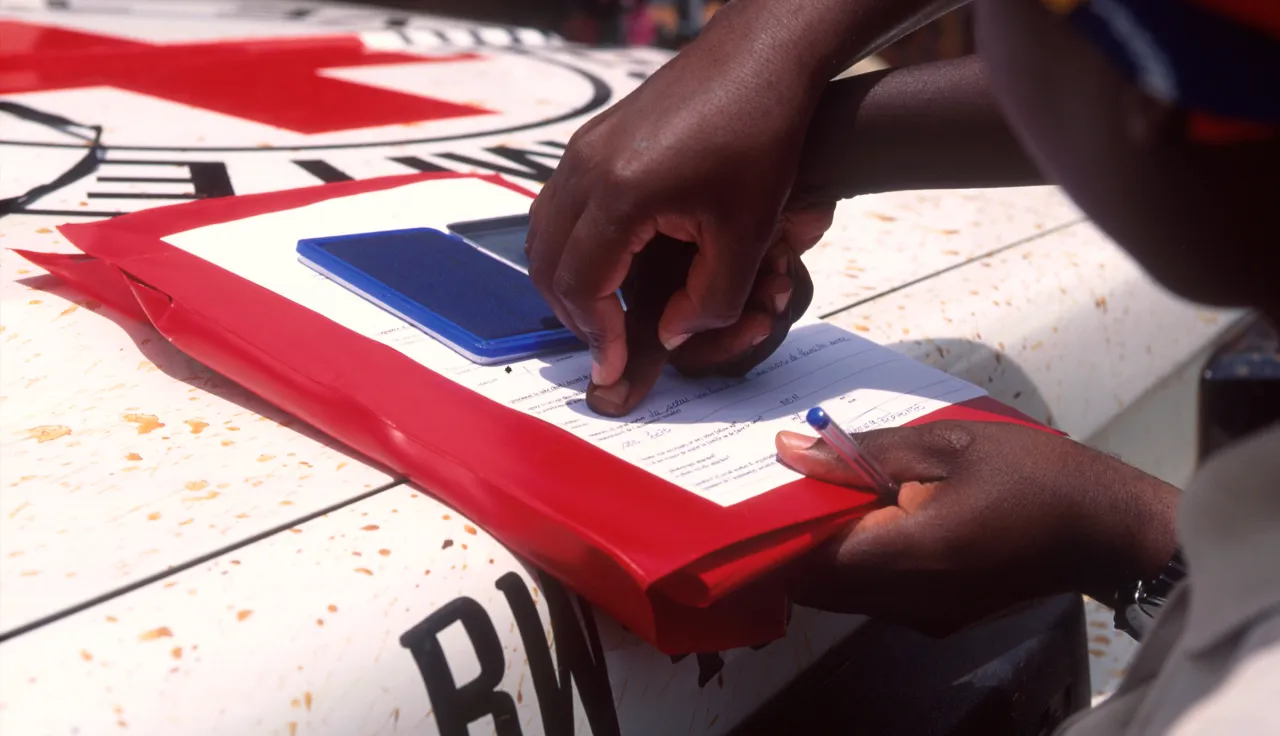
Digital Identity
Every human being has an identity. The right to identity is undisputed and recognized in international declarations and conventions. But not all human beings have a way to prove their identity.
In this regard, everyone should have a means to prove who they are through an identity tool. The form such a tool should take remains a matter of dispute. Yet no matter what its form – document, card, token, mobile app, or something else – it needs to be produced and managed.
The mandates of humanitarian organizations frame their action, and this is particularly acute with digital identity.
Connectivity as aid
In emergencies, staying connected can help beneficiaries get in touch with separated family members, plan safe routes, find shelter, engage with humanitarian organizations, and access humanitarian and other services. Yet after disasters, the telecommunications networks on which connectivity relies frequently stop working, depriving affected people of the communication channels on which they increasingly rely. Observations have shown that beneficiaries attach considerable importance to connectivity.
Social media
Humanitarian organizations interact with beneficiaries via social media in a variety of ways. In emergencies, for instance, they may use social media to inform people about safe places and the delivery of aid. They may also use social media to raise awareness (such as addressing humanitarian needs arising in the framework of migration), to encourage beneficiaries to share information with each other in an emergency, or to provide information about health and medical care. Engaging with beneficiaries in this way carries a number of risks.
When individuals view or reply to public or private social media posts by Humanitarian Organizations, or when they join public or private groups hosted by such organizations, they share a rich variety of data with the platform in question.
Artificial intelligence and machine learning
This chapter explores the data protection challenges associated with the use of artificial intelligence and machine learning systems in the humanitarian sector. Some of these challenges relate to the much-debated topic of automated decision-making, while others arise from the fact that such systems frequently rely on the heavy usage of data, sometimes including personal data.
The sections that follow first give a basic explanation of the technology in question, then identify the related data protection challenges and provide guidance for humanitarian organizations on how to address some of these challenges.
Advisory Group:
Experts from the following institutions:
Brussels Privacy Hub (VUB), International Committee of the Red Cross (ICRC), Swiss Data Protection Authority, European Data Protection Supervisor, Office of the United Nations High Commissioner for Refugees (UNHCR), International Organization for Migration (IOM), International Federation of Red Cross and Red Crescent Societies (IFRC), United Nations Office for the Coordination of Humanitarian Affairs, Yale University, Privacy International, French-speaking Association of Personal Data Protection Authorities, Swiss Federal Institute of Technology in Lausanne (EPFL), Doctors Without Borders, and Senegalese Data Protection Authority
Previous editions of the Handbook on Data Protection
Follow the Sun: A Digital Launch of the Data Protection Handbook (2nd ed.)